You can plan a route easily, but there is sadly no way to save it for later use
- 5 Posts
- 26 Comments

 0·5 months ago
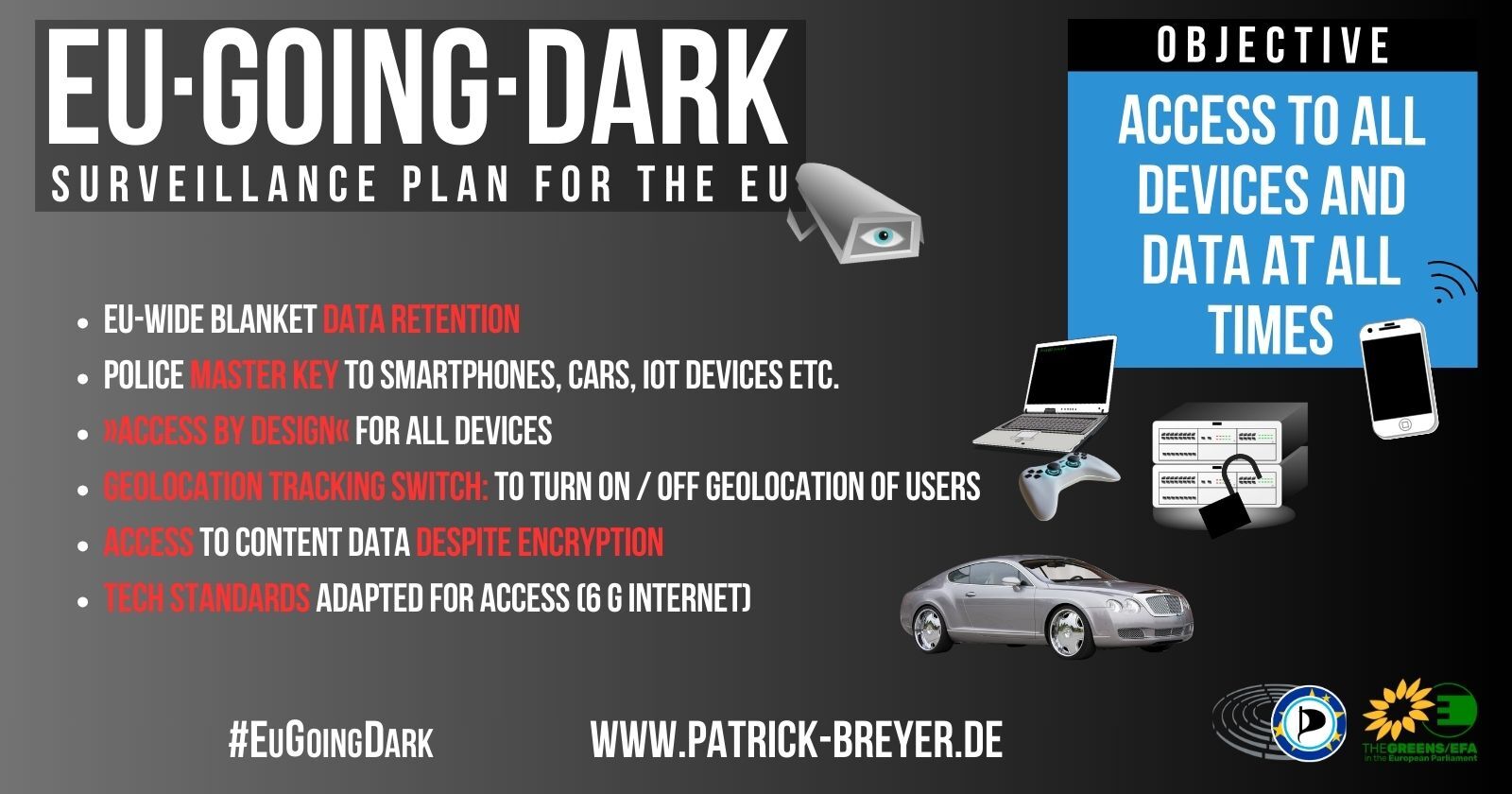
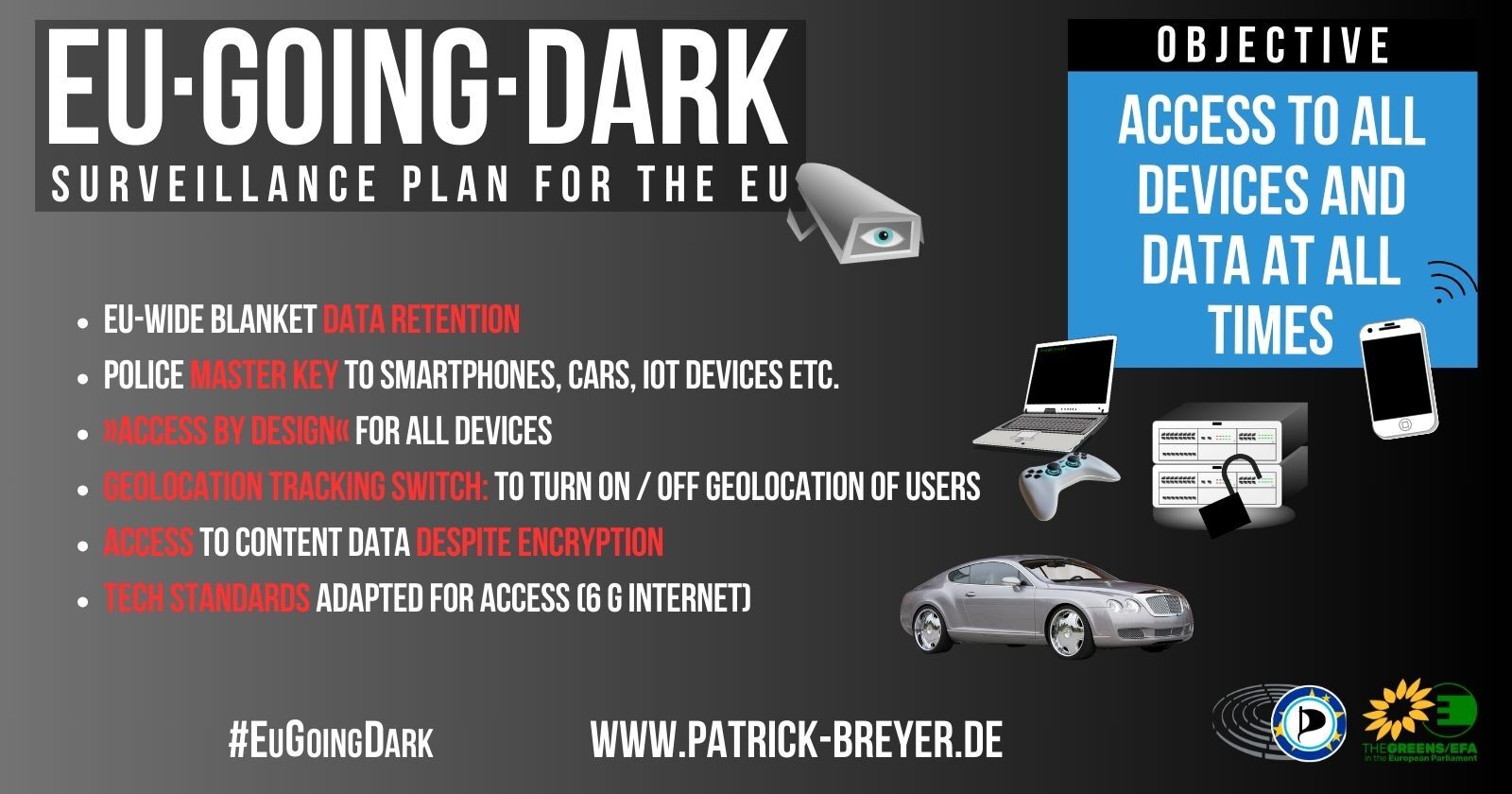
0·5 months agoYes it does, but why would that exception be needed if it was such a good infallible system that they are proposing. They know of the problems of their proposal and are not willing to have it in a corporate or their own systems but it’s supposed to be fine for the masses to have security and privacy issues

 0·5 months ago
0·5 months agohttps://www.patrick-breyer.de/wp-content/uploads/2024/06/csam_cleaned.pdf
Leaked updated proposal (14.06.2024)
(12a) In the light of the more limited risk of their use for the purpose of child sexual abuse and the need to preserve confidential information, including classified information, information covered by professional secrecy and trade secrets, electronic communications services that are not publicly available, such as those used for national security purposes, should be excluded from the scope of this Regulation. Accordingly, this Regulation should not apply to interpersonal communications services that are not available to the general public and the use of which is instead restricted to persons involved in the activities of a particular company, organisation, body or authority.
= it has stayed the same. They still want to exempt themselves

 0·5 months ago
0·5 months agoDie Kontaktdaten der jeweiligen ständigen Vertretungen der Länder in der EU sind hier zu finden. Schreibt den Vertretungen!
Wenn man keine eigene email formulieren möchte, kann man auch einfach chat-gpt o.ä. nutzen mit ein paar zeitungsartikeln als Anregung für Argumente.

 1·5 months ago
1·5 months agoI downloaded the mobile app (ios) and i don’t see any way to connect it to your own selfhosted server. You can only create an account with them. Didn’t look further, but it would be pretty weird to first have to create an account with them and only afterwards being able to connect to your own server.
Edit: The access is just deeply hidden. You have to tap 7 times on the login in screen in the app to enter developer settings. There you can enter your own server.
https://help.ente.io/self-hosting/guides/custom-server/
So yeah thumbs up from me!

 0·5 months ago
0·5 months agoIt depends on the country you live in. You will have to research that. As a rule of thumb, it is conservative/ right wing parties pushing for heavier surveillance of citizens.
As it stands right now, the Eu parliament (which consists of people who we vote in to office), is the government body which opposes these measures. But there are only a few member countries left in the parliament which do that, so our votes are important!

 0·6 months ago
0·6 months agoTldr: This is a traffic analysis attack, it exposes metadata without help or access to data from whatsapp. Other messengers are vulnerable too. It requires vast resources and access only governments have. It is not a threat model that todays messengers defend against.
The interesting part of the article ist the last one.
According to the internal assessment, the stakes are high: “Inspection and analysis of network traffic is completely invisible to us, yet it reveals the connections between our users: who is in a group together, who is messaging who, and (hardest to hide) who is calling who.”
The analysis notes that a government can easily tell when a person is using WhatsApp, in part because the data must pass through Meta’s readily identifiable corporate servers. A government agency can then unmask specific WhatsApp users by tracing their IP address, a unique number assigned to every connected device, to their internet or cellular service provider account.
WhatsApp’s internal security team has identified several examples of how clever observation of encrypted data can thwart the app’s privacy protections, a technique known as a correlation attack, according to this assessment. In one, a WhatsApp user sends a message to a group, resulting in a burst of data of the exact same size being transmitted to the device of everyone in that group. Another correlation attack involves measuring the time delay between when WhatsApp messages are sent and received between two parties — enough data, the company believes, “to infer the distance to and possibly the location of each recipient.”
Today’s messenger services weren’t designed to hide this metadata from an adversary who can see all sides of the connection,” Green, the cryptography professor, told The Intercept.
She is a Covid19 conspiracy nut. Don’t give her visibility. One example: https://youtu.be/LtFfsRoJbg8?feature=shared The title of that video is „Visit to the banks was more like a visit to a concentration camp“ during covid lockdowns

 0·6 months ago
0·6 months agoAt first i thought some reasons sounded reasonable too, but after reading the github issue i changed my mind. See my edit for reasons.

 0·6 months ago
0·6 months agoThe response by the debian maintainer responsible for this change to the keepassxc developer is an actual disgrace
Request to revert change:
@julian-klode this needs to be reverted asap. This is now our fourth bug report because of the decision to neuter the base KeePassXC package in Debian. Put the base package back where it was and create a keepassxc-minimal.
Response by debian maintainer:
julian-klode commented 9 hours ago: I’m afraid that’s not going to happen. It was a mistake to ship with all plugins built by default. This will be painful for a year as users annoyingly do not read the NEWS files they should be reading but there’s little that can be done about that. It is our responsibility to our users to provide them the most secure option possible as the default. All of these features are superfluous and do not really belong in a local password database manager, these developments are all utterly misguided. Users who need this crap can install the crappy version but obviously this increases the risk of drive-by contributor attacks.
The whole github issue is worth a read, as it actually explains the issue with the change.
Edit: as i gave the debian maintainers view visibility i wanted to give a quick summary of the keepassxc point of view as well:
-
julian-klode specifically mentions attacks by contributors of keepassxc. If you don’t trust the developers, why would you trust the minimal package which is developed by the same people?
-
If the Debian packagers have good reason to believe the keepassxc-full version presents a broader attack surface, then they ought to present what they’ve seen that makes them feel that way, not promote baseless innuendo.
-
the features are disabled by default. If you do not opt in, the code never gets executed.
-
the safest version of keepassxc is the one thats tested, meaning full featured
-
removing all those features doesn’t make it more secure, it dumbs it down to an encrypted spreadsheet and makes it less secure. Users should be automatically notified when one of their accounts has been breached and their password for that account has been found floating in a db dump. Users should rely on their password manager to handle logins for them, so they’re less likely to get tricked into a phishing page.
-
if you disagree with features in someones app you fork it. You do not change it and distribute it under the same name. A -minimal version would have been ok
-
Debians own policy is to communicate with upstream beforehand before introducing changes. This was not the case, nor was there a chance to collaborate on an effective solution for both parties.
-
Debian could have chosen to give users an informed choice between -full and -minimal. Instead they broke existing users installs.
-
People saying it was released in Debian sid, which is meant for changes. It is also meant for Feedback, which julian-klode refuses to listen to.
-
That really shouldn’t be happening, make sure to file a bug report if it’s the core themes!
Hasn’t happened to me in the years i have used KDE.

 0·6 months ago
0·6 months agoThats great to hear! Boredsquirrel is right, the download size might not matter to me, but it’s important to improve for a lot of reasons, i can see that.
Edit: For other people reading this, this is a nice read related to the download sizes and what can be done.
On a side note: keep doing what you are doing. Your blog posts and the enthusiasm you displayed in your YouTube videos are what got me interested in universal blue in the first place.
Well there’s a simple thing you are overlooking. You could just not theme Kde with third party themes and extentions and stuff like kvantum themes. It wouldn’t break, just like gnome. Still if you do decide to change stuff its going to be fine most of the time. The beauty of Kde is that there is the option to change stuff, but you aren’t required to.
KDEs default layout is really beautiful and well put together, just like gnome is.
Oh and don’t forget to take backups of your /home. Thats good practice for every desktop environment.

 0·6 months ago
0·6 months agoThat sounds like a usecase for distrobox or toolbx, and not something an average user would need to consider for choosing a distro

 0·6 months ago
0·6 months agoI agree with you, that the future of Desktop Linux are the atomic Distros. They are more stable and require less intervention, so they can be used more easily by less knowledgeable users and users who prefer a stable OS(in the non-breaking way, not no updates). Making Linux more accessible for new users, is exactly what Linux needs.
I disagree on your view about the Fedora atomic spins, especially universal blue. Who cares if the underlying OS downloads as one big image. It all happens in the background, you don’t notice that. Everytime you reboot, you are on an updated system.

 0·6 months ago
0·6 months agoYou might be pleased to hear that it’s released for ios. https://feddit.de/post/11733855
Read some of my other comments. 0-100 is more intuitive than -18-38, no? None of you have even been willing to admit that simple fact yet.
Well because it stands on a false promise. Neither 0°F = the freezing temperature of a solution of brine made from a mixture of water, ice, and ammonium chloride nor 100°F has any „real“ meaning. The other limit established was his best estimate of the average human body temperature, originally set at 90 °F, then 96 °F . How is that intuitive.
If you are refering to negative degrees, quite useful for telling how the weather is going to be. And to prevent the „negative numbers are hard“-Argument. It seems to work for the majority of people.
For the human bodytemperature argument often throw around: they are inconsiquential numbers in both systems.
Multiple problems with you assertions.
A) Fahrenheit has an appropriate level of granularity for humans
You know that Celsius uses decimals for everything, so really not much difference. Furthermore the granularity of Fahrenheit doesn‘t have any advantages. You won‘t be able to feel wether its 70°F or 71°F outside, nor if you’ve got a fever of 101°F or 102°F. You need to look at a thermometer. And please don‘t reply saying that decimals are complicated. The majority of the planet, except certain Countries seem to manage just fine. Would be quite laughable if one certain country thinks it‘s too complicated.
B) Fahrenheit has an intuitive frame of reference for humans
Not really sure what you are referencing. I think it just stems from you growing up with Fahrenheit, so not feeling comfortable with anything else.
But Fahrenheit is the temperature scale of the proletariat, the working man, the average Joe. And I’m here for it.
I mean the “proletariat” of the majority of the world uses Celsius.

 0·8 months ago
0·8 months agoI don‘t think that article says what you think it says. First we need to accept your comparison and generalize the study to question wether law enforcement will treat you differently because of political views. And then it clearly states that the LOE treated the participants differently (negatively), because of the political views:
„Nevertheless, he concluded that it is statistically unlikely that this number of previously ‘safe’ drivers could amass such a collection of tickets without assuming real bias by police against drivers with Black Panther bumper stickers.“
Note that the “Nevertheless“ is in the context of the police only using the political bumper stickers as reason for citation only once. The rest of the citations were for other reasons. The participants had not been cited in all their driving in the year prior without the stickers. This leads to the mentioned statement by the author


I think the feature request is a way to record your travel right? I thought you meant more of a way to plan the route ahead of time and save it, so you can come back to it at any time.